By Dave Millier / February 02, 2026
Latest Blog
By Dave Millier / March 02, 2026
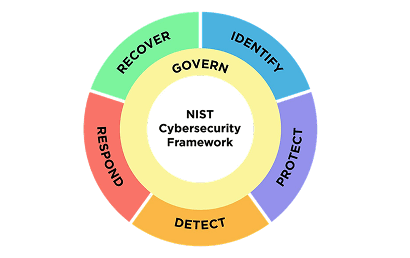
Cybersecurity has crossed a threshold. Organizations are no longer asking whether they need monitoring. The real question now is whether their security operations can keep up with the speed, scale and persistence of modern attacks.

By Dave Millier / February 02, 2026
By Felicia Gopi / December 29, 2025

By Felicia Gopi / December 02, 2025

By Felicia Gopi / October 29, 2025
By Felicia Gopi / September 22, 2025

By Felicia Gopi / September 02, 2025
By Felicia Gopi / August 05, 2025

By Dave Millier / July 21, 2025
By Dave Millier / July 21, 2025